Table Of Contents

Welcome back to our exploration of the intricate world of sensitivity labels! In this segment, we’ll delve into a crucial aspect of sensitivity labels: Conditions. Buckle up, because we’re about to take a deep dive!
Understanding Conditions
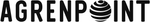
Conditions play a pivotal role in sensitivity labels, dictating when and how labels are applied to items. These conditions encompass a variety of criteria, from content types to specific patterns or keywords within documents or emails. One important feature tied to the conditions is client-side auto-labeling. With this feature, you have two options:
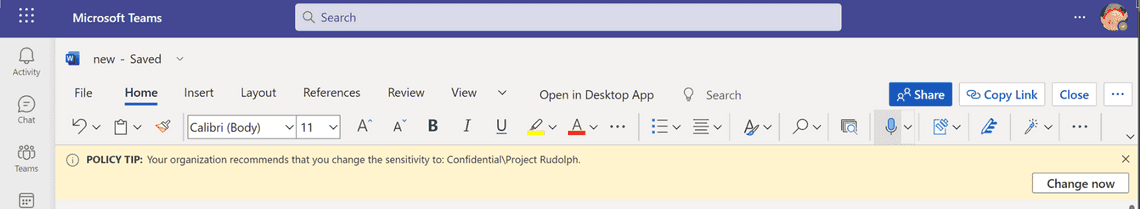
- Suggested Labels: Users receive label suggestions, allowing them to make informed decisions about sensitivity.
- Automatic Label Application: Labels are applied automatically based on predefined rules.
Client-Side vs. Service-Side Labeling
Before we delve further into Conditions, let’s briefly touch upon the distinction between client-side and service-side labeling. Client-side labeling can auto-apply sensitivity labels while editing documents in Word Online or the desktop app. When specific conditions (configured in auto-labeling settings) are met, the label is either automatically applied or recommended to the user.
Service-side labeling is about automatically applying rules to Data at Rest, such as uploaded content in SharePoint and OneDrive. We will look at autolabeling policies another time.
Now, let’s examine an example JSON representation of Conditions, showcasing the intricate configuration involved:
{"And": [{"Or": [{"Key": "CCSI","Value": "687236ed-b249-4349-9fef-a8cbd7b590f9","Properties": null,"Settings": [{"Key": "mincount","Value": "1"},{"Key": "maxconfidence","Value": "100"},{"Key": "groupname","Value": "Default"},{"Key": "rulepackage","Value": "5DA58D7A-25F1-4205-93D0-BEB10054C503"},{"Key": "name","Value": "Project Rudolph SIT"},{"Key": "minconfidence","Value": "85"},{"Key": "maxcount","Value": "-1"},{"Key": "policytip","Value": "This file contains information regarding the Project Rudolph. A sensitivity label has been suggested to protect the data"},{"Key": "confidencelevel","Value": "High"},{"Key": "autoapplytype","Value": "Recommend"}]}]}]}
Incorporating Conditions into Label Management
Now that we’ve gained a deeper understanding of Conditions and their role in sensitivity labeling, let’s explore how they can be leveraged to craft customized labels tailored to an organization’s unique requirements. With PowerShell, administrators can manipulate Conditions to define intricate labeling policies, ensuring sensitive information is appropriately protected across various content types and scenarios.
Create a new label using conditions from another existing label
In the previous post we created a new label were we took the shortcut and used the internal properties for creating a new label. We can do the same thing here and piggyback off that, this will be a smaller example so you understand. And this is what we are trying to achieve for the end-user:
$LabelParams = @{Name = "InternalTest"DisplayName = "InternalTest"Tooltip = $label.TooltipConditions = $label.Conditions}
Update a label to use another SIT
$sit = Get-DlpSensitiveInformationType "Sweden Passport Number"
Then we change the rulepackID, the name and the policytip.
$label.Conditions = @"{"And": [{"Or": [{"Key": "CCSI","Value": "687236ed-b249-4349-9fef-a8cbd7b590f9","Properties": null,"Settings": [{"Key": "mincount","Value": "1"},{"Key": "maxconfidence","Value": "100"},{"Key": "groupname","Value": "Default"},{"Key": "rulepackage","Value": "00000000-0000-0000-0000-000000000000"},{"Key": "name","Value": "Sweden Passport Number"},{"Key": "minconfidence","Value": "85"},{"Key": "policytip","Value": "This file contains information regarding Swedish passport"},{"Key": "maxcount","Value": "-1"},{"Key": "confidencelevel","Value": "High"},{"Key": "autoapplytype","Value": "Recommend"}]}]}]}"@
And finally, we update the label using the changed conditions.
$LabelParams = @{Identity = "InternalTest"Conditions = $label.Conditions}Set-Label @LabelParams
Thank you for reading
/Simon